It is 2023 and not much has changed in respect to warning people about phishing. For over 20 years, I have been telling people the same thing, “Don’t open emails from people you don’t know.” Fast forward to 2023 and that is still true. Threat actors are impersonating people we know, which has created a shift in our thinking toward email. In fact, phishing attempts increased by 61% in 2022 over the previous year (State of Email Security 2023) and 84% of organizations faced at least one successful phishing attack in 2022 (Proofpoint 2023 Report).
We still shouldn’t open emails from people we don’t know, but that is no longer enough. Now, the thought has to be “question every email.” That may seem like a daunting task, but proper and continuous training will help filter most legitimate emails from phishing attacks relatively quickly.
The security awareness training program developed ten years, or even five years, ago is probably outdated and not designed to keep pace with the advances that threat actors have made in phishing attacks—and the attacks are only going to increase.
Sitting through a one- to two-hour security awareness training session once a year does not adequately prepare employees for dealing with the threat landscape of today. Think of it another way: if you were NASA and wanted a successful mission to Mars, would you train the astronauts on mission critical task for one hour in a year? Probably not.
Advances in technology have given threat actors the ability to become more sophisticated in their attacks, spoofing email addresses and obfuscating information in the message header to bypass detection. Oddly enough, it is the simple phishing attempts that often have the most success.
More and more, we are seeing QR codes embedded in phishing emails to compromise a device or drive someone to a malicious site. Attackers often deploy a “spray and pray” technique, sending out hundreds of thousands of phishing emails hoping someone will open the attachment in the email or click on the link. Once you do, they have you.
So how do you avoid falling prey to a phish? Train more often, apply the fundamentals of security awareness training and read, don’t scan, your emails. Here are a few things to indicate a suspicious email:
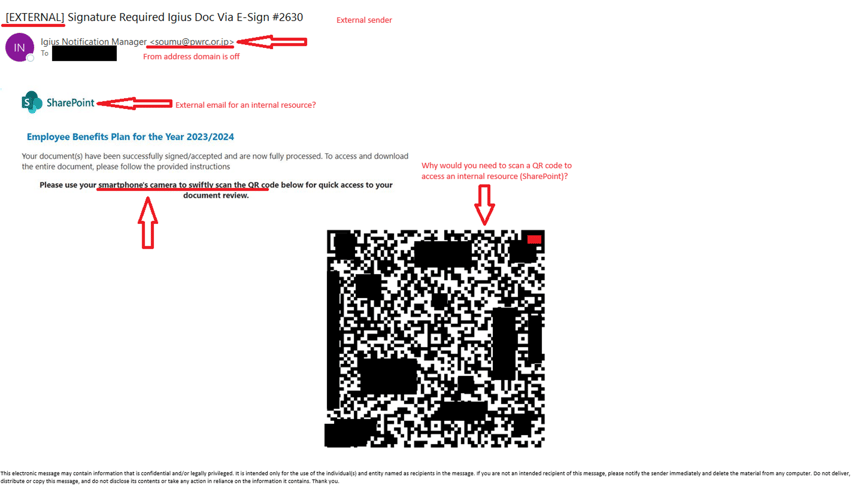
- Sender’s name does not match the email address in <sender’s email>.
- The email was not expected.
- There's a heightened sense of urgency to get you to do something.
- The message composition is unusual. Does the sender normally write this way?
- They are asking for information they should already have.
- The message originated from an external source, but should have come from an internal source if it were legitimate.
- Are you prompted to perform some action to complete a task?
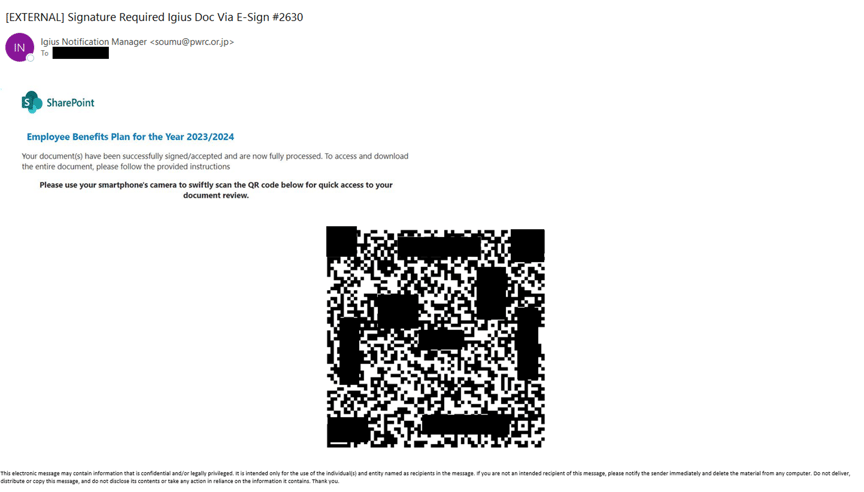
Here is an example of a real-world phishing attempt, the recipient’s name and email address have been redacted. Notice anything unusual?
Here is the same message with some red flags indicated. Were you able to identify the indicators of a potential phish?
Security awareness training is not a “one and done”. Continuous training that evolves with the threat landscape will keep you alert and your phishing detection skills honed.
“We don't rise to the level of our expectations, we fall to the level of our training.” - Archilochos
Learn more about our Cybersecurity Services, including Awareness Training and Virtual CISO services, at IGIcybersecurity.com.

